TL-NFW6430 is an enhanced firewall product launched by TP-LINK, which supports anti-virus, intrusion prevention, malicious domain names, application identification, website classification and other characteristic libraries, and integrates firewall policies, attack protection, DPI in-depth security, security audit, bandwidth management, VPN and other functions, effectively resisting network risks, achieving comprehensive protection, simplifying operation and maintenance, and ensuring the continuous and stable operation of enterprise core applications and services. Scenarios such as network compliance construction.
- Quad-core ARM architecture 64-bit network-specific processor, main frequency 2.2GHz, 4GB DDR4 high-speed memory
- 4 x 2.5G RJ45 ports, 16 x Gigabit RJ45 ports, 8 x Gigabit SFP ports, 2 x 10 Gigabit SFP+ ports, 1 x HDD interface (HDD/SSD)
- Expandable all-in-one DPI security (intrusion prevention, anti-virus, file filtering, malicious domain name remote query, application behavior control)
- Supports rich policy objects (security zones, addresses, applications, blacklists and whitelists, security profiles, intrusion prevention, audit profiles, etc.)
- You can configure security policies, audit policies, bandwidth policies, and NAT policies
- Supports rich network functions, such as static routing, policy-based routing, intelligent balancing, VPN (IPSec/PPTP/L2TP VPN), DDNS, etc
- Supports first-pack application identification to improve application recognition performance
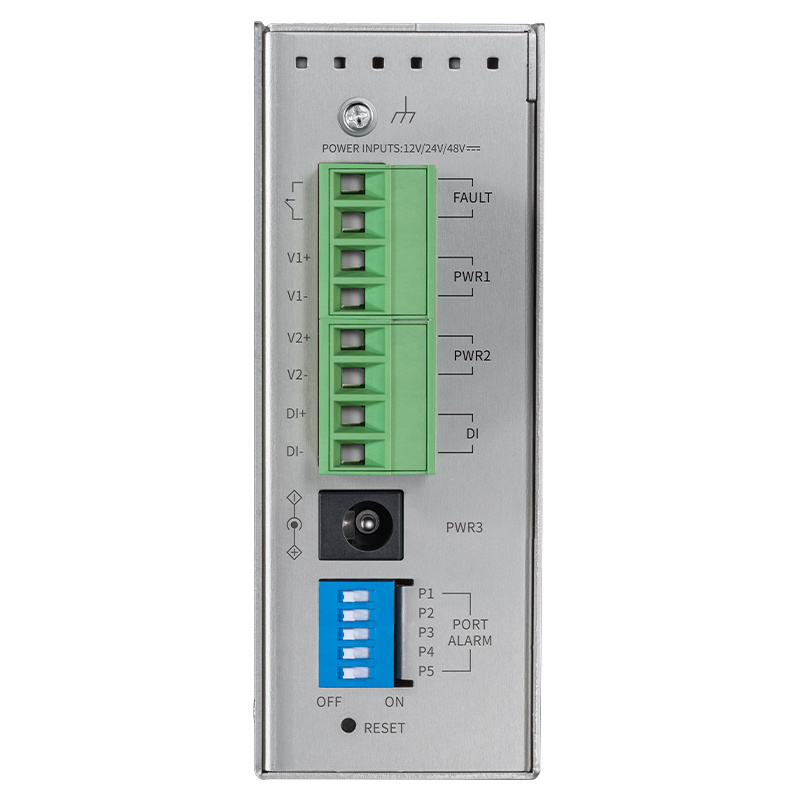
Abundant ports and powerful performance
It adopts a professional multi-core 64-bit network dedicated processor, with a main frequency of 2.2GHz and 4GB DDR4 high-speed memory, providing powerful packet processing capabilities.
It provides 4 2.5G RJ45 ports, 16 Gigabit RJ45 ports, 8 Gigabit SFP ports, 2 10 Gigabit SFP+ ports, and 1 hard disk interface (HDD/SSD), which is convenient for users to manage and maintain the system while meeting the requirements of high-speed data forwarding.
First-pack application identification
It supports TP-LINK's unique application identification of the first packet, which can identify the application in the first packet, realize application traffic selection, and improve the application recognition performance
High availability
Support dual 100W pluggable redundant power supply: 1+1 redundancy to ensure that the firewall is always online;
One pair of RJ45 bypass ports is supported, and business data is not interrupted due to firewall device failures.
Active/standby switchover: Two firewall devices can be switched over active/standby, and when a fault is detected, service data is automatically switched to the standby server for rapid recovery.
Dual-mirror mode: The firewall will automatically detect the running status of the current system and switch to the standby system once it is detected as unavailable, so that the user/service is not aware of it.
Support emergency mode: in addition to the standing dual system, it comes with an upgrade system, when the dual systems are down due to failure, the equipment system can be refreshed through the small system, and the on-site recovery does not have to be returned to the factory for maintenance. Reduce failure recovery time.
Equipped with "TP-LINK Cloud Exhibition", private network-level SD-WAN networking experience
The underlay and overlay layers provide a variety of networking architectures for access points such as headquarters, branches, and clouds of large, medium, and small enterprises to meet diverse interconnection requirements such as remote networking, remote office, and distributed security, and improve network efficiency
Authorized Cloud Security*-Perimeter Defense Service is supported
Network equipment is on the cloud, and unified operation and maintenance in the cloud is in the cloud. Real-time perception of the situation to reduce labor costs; Increase the speed of reflection and flexibly adapt to the development layout of the enterprise;
Support cloud management and control of enterprise networks, remotely block attack sources, isolate compromised terminals, and block malicious virus files;
It supports cloud security domain management, allowing devices in the same security domain to access each other, and open security policies are required to open security policies for mutual access between devices in different security domains, so as to improve the security and resilience of enterprise networks by reasonably dividing security domains and deploying resources.
Attack sources can be blocked by IP address or domain name, and all known attack sources can be automatically filtered to reduce the link load. Suspicious addresses can be pre-stored in the blacklist, and manually released after the risk is eliminated. Relevant information will be retained for the IP addresses or endpoints that appear in the blacklist, so that risks can be quickly located in the future and meet the needs of refined access control.
Provides a multi-dimensional security log statistics dashboard and one-click export of security logs in the cloud. It supports fine-grained log retrieval, up to 22 search conditions, and provides full-dimensional, cross-device, and visual log analysis to assist users in comprehensively auditing the overall security status of the information system.
*The self-owned cloud platform meets the requirements of Level 3 of classified protection
Comprehensive security strategy
Adopting the principle of minimum security, it supports security policies based on security zones, source IP addresses, destination IP addresses, source ports, destination ports, service groups, application groups, user groups, time periods, blacklists and whitelists, websites, internal server certificates, anti-virus, URL filtering, file filtering, application behavior control, email content filtering, intrusion prevention, audit profiles and other objects.
All-round attack protection
It supports a variety of intranet/extranet attack protection functions, and can effectively prevent various DoS attacks, scanning attacks, and suspicious packet attacks, such as TCP Syn Flood, UDP Flood, ICMP Flood, IP Scanning, Port Scanning, WinNuke Attacks, Fragment Packet Attacks, WAN Port Ping, TCP Scan (Stealth FIN/Xmas/Null), IP Spoofing, TearDrop, etc.
ARP protection, such as ARP spoofing and ARP attacks, is supported to avoid service interruption and frequent network disconnection.
Support IP and MAC binding, which can bind the IP and MAC address information of the LAN port (intranet) and WAN port (extranet) hosts at the same time to prevent ARP spoofing.
MAC address filtering is supported to block access to unauthorized hosts.
Expandable integrated DPI for in-depth security
Support intrusion prevention, get the latest threat information in the first time, and accurately detect and defend against attacks against vulnerabilities;
It supports anti-virus, which can quickly and accurately detect and kill viruses and other malicious programs in network traffic, and protect more than 6 million viruses and Trojans.
It supports filtering file expansion types, which can easily filter all kinds of small files embedded in web pages to prevent viruses and Trojan horses from invading the enterprise network through small files and endangering network security.
Support URL filtering, remote query of malicious domain names, effectively intercept phishing websites, Trojan attacks, hacker intrusions and network fraud through local + cloud methods;
It supports application recognition, and the accuracy reaches the level of application behavior. The combination of application identification and intrusion detection, anti-virus, URL filtering, and filtering file expansion types greatly improves the detection performance and accuracy.
Provide a comprehensive and timely security signature database, keep up with the latest developments in the field of network security, and ensure timely and accurate updates of the feature database.
Refined identification and control of online behaviors
It has a large-scale application identification feature database, and one-click control of nearly 6,000 common desktop and mobile Internet applications in 36 categories, including video, social networking, shopping, finance and other applications;
Accurately identify popular application behaviors such as WeChat, Weibo, and QQ, such as text communication, voice and video, file transfer, music playback, etc., and finely control these behaviors, and intercept or restrict them in a purposeful and targeted manner;
Built-in database of more than 10 types of domestic URLs, which can restrict employees' access to the corresponding websites with one click;
Support prohibiting web submission, restricting employees from logging in to various web-based forums, microblogs, mailboxes, etc. to publish information, filtering email content, and effectively avoiding the leakage of sensitive enterprise data;
*The database of applications and URLs will be updated and added continuously.
Complete security audit strategy
Detailed and comprehensive logging: System logs, operation logs, policy hit logs, traffic logs, audit logs, threat logs, content logs, URL logs, and email filtering logs are supported to record firewall-related traffic and operation history in detail, helping administrators understand network status and quickly locate network problems.
Graphical traffic statistics: Traffic statistics can be performed in three dimensions: interface, IP, and security policy, and the traffic data of security policies can be displayed graphically in real time, which is clear at a glance. The traffic analysis report can be output in the form of PDF report to help the administrator analyze the historical traffic distribution.
Internet behavior audit: Support HTTP behavior audit, FTP behavior audit, email audit, IM audit, through audit logs, you can understand the Internet behavior of employees during work, including web access, APP application, etc., so that bad Internet behavior can be traced;
TP-LINK security audit system: It can be used with the TP-LINK security audit system to store logs for a long time and in large capacity, and output more detailed analysis reports.
Simple O&M and security management
Full Chinese web interface, detailed and clear configuration guidance;
Graphical interface display, real-time monitoring of key resources such as CPU utilization, clear and intuitive;
Support local/remote management, convenient chain operation, remote assistance;
Support password authentication/identity recognition to ensure authorization security;
Support multi-administrator roles and refined permission management;
Support hard disk management, license management, and signature database upgrade;
Support active/standby switchover and on-line detection to ensure high-reliability operation of the equipment;
A separate console management port is provided, which can be managed from the command line.
Flexible bandwidth management policies
Provides flexible bandwidth management policies to control the bandwidth used by each IP address in the network to ensure the network experience of key services and users. The management and control methods include bidirectional bandwidth control, connection limit, and connection monitoring.
Abundant routing features
Static routing, policy-based routing, intelligent balancing, VPN (IPSec/PPTP/L2TP VPN), dynamic DNS (Peanutshell, Kemai, 3322) and other functions are supported.
Supports multiple deployment modes
Layer 3 routing gateway mode
As a Layer 3 routing gateway, TL-NFW6430 replaces the original router in the network, and the data communication between the internal network and the external network is NAT converted through the firewall.
Layer 2 transparent bridge mode
TL-NFW6430 allows some or all of the interfaces to be set up as bridges, which work in a Layer 2 network and are protected by firewalls as long as data passes through the bridge interfaces. In this mode, firewall deployment does not need to change the original topology, which is more convenient and faster.
Route + Bridge mode
During actual network deployment, some interfaces of the firewall can be set as bridge interfaces and part of the firewall interfaces as routing interfaces according to on-site requirements, so that the two methods can be flexibly combined to achieve more cost-effective network protection.
Hardware specifications
| Port |
|
| Dimensions |
|
| Enter the power supply |
|
| Use environment |
|
| Processor |
|
| Memory |
|
| SSD |
|
| FLASH |
|
| Heat dissipation |
|
Software Features
| High availability |
|
| TP-LINK "Cloud Exhibition" |
|
| Cloud Security - Perimeter Defense |
|
| Cloud Security - Healthy Internet Service |
|
| All-in-one DPI for in-depth security |
|
| Attack protection |
|
| Network Capabilities |
|
| Policy configuration |
|
| Policy Objects |
|
| System administration |
|
Performance Parameters*
| Maximum number of concurrent connections |
|
| New Connection Rate (Connections/s) |
|
| Network layer throughput (1518/512/64 bytes, UDP) |
|
| Application Layer Throughput (Mbps) |
|
| Application Recognition Throughput (Mbps) |
|
| IPS Throughput (Mbps) |
|
| Total Threat Throughput (Application Identification + IPS + AV + Malicious Domain Name) (Mbps) |
|
| *Parameter description |
|
Compatible hard drives
| Western Digital |
|
| Toshiba |
|
| Seagate |
|
Optional information
License (TL-FW-LIS-ALL-E, All-in-One)*
| IPS library |
|
| AV library |
|
| Malicious domain name library |
|
| App Gallery |
|
| Website Library |
|
| *Parameter description |
|
License Authorization (Separate License)*
| TL-FW-LIS-IPS |
|
| TL-FW-LIS-AV |
|
| TL-FW-LIS-URL |
|
| TL-LIS-APP |
|
| TL-LIS-URL |
|
| *Parameter description |
|
4.9
12 views
Reviews
Reviews
Q How to make a payment?
E****R 18/11/2024
A We accept various payment methods including bank transfers, credit cards, and PayPal. Please refer to our payment page during checkout for detailed instructions on how to complete your payment. If you have any questions or need assistance with payment, please contact our customer support team.
18/11/2024
Q How will the products be shipped?
T****k 16/08/2024
A We ship products through reliable courier services such as DHL, UPS, and FedEx. Shipping fees and delivery times may vary depending on the destination. You will receive a tracking number once your order has been dispatched, allowing you to track the status of your shipment. Please note that shipping times may vary based on location and availability.
16/08/2024
Q How is warranty provided?
L****Y 08/05/2024
A We offer a warranty on all of our products. The warranty period and conditions vary depending on the product category. For specific warranty information, please refer to the product page or your purchase agreement. If you encounter any issues with a product during the warranty period, please contact our customer service team with your proof of purchase, and we will guide you through the warranty claim process.
08/05/2024

































★ ★ ★ ★ ★ 16/08/2024
Good service!
(156)
★ ★ ★ ★ ★ 23/07/2024
Good!
(982)
★ ★ ★ ★ ★ 23/07/2024
Good quality!
(982)